December 8th, 2022 by Function4
Dark web scanning is particularly important for businesses because of the potential risk posed by data breaches. The dark web is a collection of websites and networks that are not indexed by search engines, making it difficult to detect or monitor...
Read Full Story »
Tags: cyberattacks, dark web, managed IT, risk management, services, solutions
Posted in: Cybersecurity
August 29th, 2022 by Kevin Box
Your organization is continuously creating confidential, valuable data that's critical to it running optimally and efficiently in real-time. And you're probably using multiple security methods–including authentication, encryption, and monitoring–to...
Read Full Story »
Tags: antivirus, copier services, cyber security, cyberattacks, risk management, solutions
Posted in: Cybersecurity, Managed Print Services
July 25th, 2022 by Function4
The modern world is a world of computers and technology. Over the years, we have flourished and achieved outstanding accomplishments in many aspects, and technology is one of them.
However, while technology has flourished, so has the prevalence...
Read Full Story »
Tags: antivirus, cyber security, cyberattacks, data backup and recovery, ransomware, risk management
Posted in: Cybersecurity
August 10th, 2021 by Kevin Box
On April 29th, 2021, Cyber Criminals were able to hack the largest fuel pipeline in the U.S. because of one password floating around on the dark web, which an employee had previously used to access the organizations' network through a Virtual Private...
Read Full Story »
Tags: cyberattacks, multifunction printers (MFP), risk management
Posted in: Cybersecurity
July 13th, 2021 by Charlie Osborne
Antivirus software isn’t enough to protect our devices and accounts any longer, but it still provides a key layer of defense.
Over the past few years, consumers and enterprises alike have become more aware of the importance of adequate cybersecurity...
Read Full Story »
Tags: antivirus, risk management, tips & training
Posted in: Cybersecurity
June 10th, 2021 by Garrett Hollander
Because of the ongoing COVID-19 pandemic, more people are working remotely than ever before. On the one hand, productivity hasn't really suffered as there are a large number of cloud-based tools that make it possible to be just as productive outside...
Read Full Story »
Tags: COVID-19, cyberattacks, remote working, risk management
Posted in: Cybersecurity
May 18th, 2021 by Nick Pegley
The IT landscape is in a constant state of change. Whether it’s still seen as a supportive administrative function, an enabler of digital transformation, or an integral touchpoint woven within everyday interactions, it is critically important to...
Read Full Story »
Tags: cloud-based, remote working, risk management
Posted in: Business Technology
May 11th, 2021 by Akisa Matsuda
It is no secret that in this age of new normality, increased security threats such as phishing or ransomware attacks, are a very real concern. Almost all devices are prone to cybersecurity threats and office printers and multifunction devices...
Read Full Story »
Tags: COVID-19, multifunction printers (MFP), ransomware, remote working, risk management, tips & training
Posted in: Cybersecurity
April 6th, 2021 by Tom Darnall
Corporate printing costs can get expensive. These costs can amount to as much as 3% of annual revenue (some estimates even go as high as 12%). It’s important to keep those costs in check. And with print security becoming an increasingly urgent priority...
Read Full Story »
Tags: cost reduction, multifunction printers (MFP), risk management
Posted in: Business Technology
March 24th, 2021 by Garrett Hollander
What is a Document Management System (DMS)?
What is a document management system? Put simply, a document management system is an automated business software solution used to organize, secure, store, capture, digitize, and tag business files....
Read Full Story »
Tags: cloud-based, cost reduction, digital workflows, M-Files, metadata, on-premise, remote working, risk management
Posted in: Document Management, Business Technology
March 16th, 2021 by Steve Kelley
In 2019, the online training platform Skillbox sent a rogue print job to unsecured network printers. To do that, they relied on a search tool called Shodan that discovers vulnerable Internet-connected devices. It was the very same tool that a prankster...
Read Full Story »
Tags: cost reduction, government agencies, PrinterLogic, risk management, tips & training
Posted in: Cybersecurity, Document Management
March 3rd, 2021 by Ross Lasley
The software industry has been rapidly changing over the last several years. The most significant change has come in adapting software as a service instead of selling perpetual licenses with maintenance agreements. Microsoft was one of the first...
Read Full Story »
Tags: Microsoft, mobility, risk management, SaaS
Posted in: Business Technology
February 26th, 2021 by Kevin Box
Contact a Solutions Expert
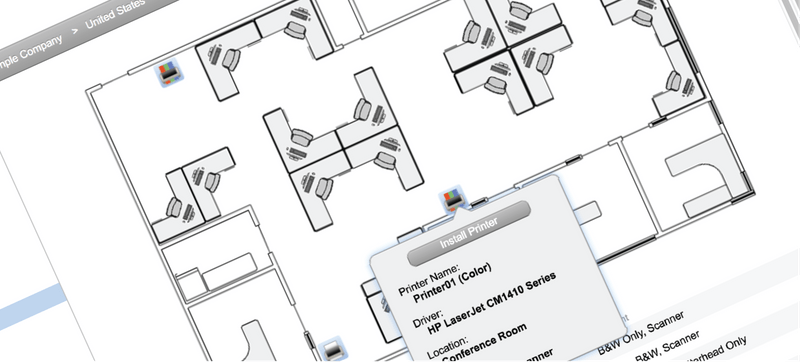
There was a time in history where the "On-trend" method for managing copier and printer fleets was to map out the office and strategically place workgroup copiers & printers within the office space to maximize...
Read Full Story »
Tags: cost reduction, enterprise, multifunction printers (MFP), risk management
Posted in: Cybersecurity, Business Technology
February 11th, 2021 by Wendy Seykens
The following article is a guest post by Wendy Seykens, Marketing and Communications Coordinator with M-Files partner BMconsultants.
This year has become the year of virtual meetings — where we all convene together to discuss business. An hour here,...
Read Full Story »
Tags: M-Files, Microsoft, content & process management, remote working, risk management
Posted in: Document Management
January 27th, 2021 by Brian Wistisen
Contact a Solutions Expert
As IT professionals are looking to move away from legacy print solutions, the idea of a serverless print infrastructure is becoming more widespread. That's true even in large enterprise organizations, where print servers were...
Read Full Story »
Tags: cost reduction, multifunction printers (MFP), PrinterLogic, risk management, SaaS
Posted in: Business Technology
January 21st, 2021 by Adam Vervaeke
Cloud communications adoption was already on the rise even before 2020. The year-over-year market growth rate for Unified Communications as a Service (UCaaS) from 2018 to 2019 was 17.7 percent, with global revenue reaching $10.4 billion in Q4. Today,...
Read Full Story »
Tags: collaboration tools, contact center, COVID-19, remote working, risk management
Posted in: Phone Systems
January 19th, 2021 by Max Queen
As a small or medium-sized business (SMB) owner, you wear many hats. One of those responsibilities may be IT security, although you may have a nagging suspicion that your company is not adequately protected. With cyberattacks continuing to escalate,...
Read Full Story »
Tags: cost reduction, cyberattacks, data backup and recovery, risk management, small & medium-sized businesses (SMB)
Posted in: Business Technology
January 12th, 2021 by Max Queen
How much will it cost your company to recover following a data breach? New research from IBM Security paints a sobering picture, with costs increasing by 450,000 on average from 2019 to 2020. And here in the U.S., businesses can expect to pay even more...
Read Full Story »
Tags: cyberattacks, data analysis, data backup and recovery, managed IT, multifunction printers (MFP), risk management
Posted in: Cybersecurity
January 6th, 2021 by Max Queen
Iconic heists have made and destroyed fortunes. They make great scenes for exciting movie plots. Think of Butch Cassidy and his gang blowing up train tracks and fleeing on horseback with $50,000 in cash. Or consider a thief walking out of the Louvre...
Read Full Story »
Tags: cyberattacks, ransomware, risk management
Posted in: Cybersecurity
December 17th, 2020 by Brad Yocum
When many technology companies are broadening their scope of services, one of the most common is hardware organizations providing IT Support Services. At first thought, this may not seem like an easy transition. The technical requirements may appear to...
Read Full Story »
Tags: managed IT, multifunction printers (MFP), risk management
Posted in: Business Technology
December 10th, 2020 by Brad Yocum
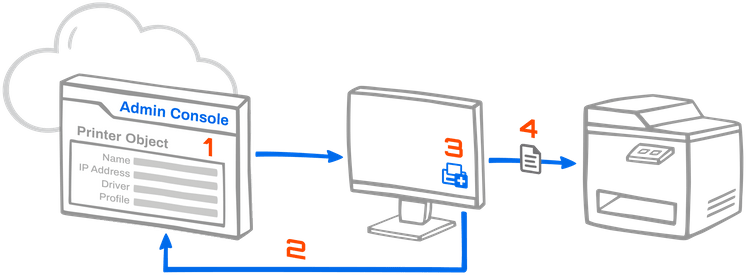
In today's environment of remote workforces and shuffling of staff to different locations throughout the office, supporting employee's technology needs can be very challenging. One of the biggest ongoing challenges for the IT department is the print...
Read Full Story »
Tags: cost reduction, managed IT, mobility, multifunction printers (MFP), risk management
Posted in: Business Technology
November 11th, 2020 by Ed Hoffmann
DARK WEB SCANNING: WHY IT IS IMPORTANT?
Have you heard of the dark web? It’s the hidden part of the internet where the illegal activity takes place online. The dark web has become a hotspot for criminals who want to sell your data. Fortunately, dark...
Read Full Story »
Tags: cyberattacks, Google, healthcare, risk management
Posted in: Cybersecurity
November 10th, 2020 by Christian Colasono
In today’s increasingly evolving print/imaging technology industry, it is of the utmost importance to know what to look for, avoid, and what questions to ask when selecting your next technology partner.
One of the most essential and overlooked areas...
Read Full Story »
Tags: content & process management, risk management, tips & training, vendor / partner relationships
Posted in: Business Technology
October 27th, 2020 by Glyn Morgan
When I started in this industry, most copiers were still using liquid toner and premix. You could always tell who had utilized these devices by the stains on the carpet in front of them. Once copiers transitioned over to dry ink, people were delighted....
Read Full Story »
Tags: cloud-based, digital workflows, mobility, multifunction printers (MFP), risk management
Posted in: Business Technology
September 16th, 2020 by Brad Yocum
For many years now, we have all heard the term “Digital Transformation.” .” What does that mean to our organization? Can we survive without paper? What is the cost, and can my staff even adopt the concept? There are so many questions that must go thru...
Read Full Story »
Tags: data analysis, managed IT, metrics, paperless, remote working, risk management
Posted in: Business Technology
July 22nd, 2019 by Function4
Do you worry about a cybersecurity breach impacting your business? These threats to cybersecurity are increasingly common, as hackers become more sophisticated and bolder in their attacks. Data breaches are destructive to your customers and your company’s...
Read Full Story »
Tags: cyberattacks, data analysis, ransomware, risk management, tips & training
Posted in: Cybersecurity
April 29th, 2019 by Function4
With all of the responsibilities that come with small business ownership, it’s easy to neglect cybersecurity. However, the cost of a data breach is simply too high to ignore. A single data breach could destroy your company’s revenue and reputation —or...
Read Full Story »
Tags: cyberattacks, risk management, small & medium-sized businesses (SMB)
Posted in: Cybersecurity
April 15th, 2019 by Function4
Mobile device usage in the workforce is now commonplace, with an increasing number of workers turning to personally or company-owned mobile devices to perform daily tasks. The benefits for employers are well established, including those in the healthcare...
Read Full Story »
Tags: healthcare, mobility, risk management
Posted in: Business Technology
April 3rd, 2019 by Function4
When you leave the office each evening, you probably lock the doors and set the security alarm. This seems obvious since you don’t want criminals breaking into your business. But do you treat cyberthreats with the same caution? After all, you probably...
Read Full Story »
Tags: cost reduction, cyberattacks, government agencies, risk management
Posted in: Cybersecurity
March 13th, 2019 by Function4
IT security issues are on every business leader's mind, or they should be. For every high profile cyberattack, there are thousands more that never make the headlines. Where does your company stand?
With small and midsize businesses (SMBs) now a favorite...
Read Full Story »
Tags: cyberattacks, managed IT, risk management, small & medium-sized businesses (SMB)
Posted in: Cybersecurity
March 11th, 2019 by Function4
If you’re a small business owner, you probably don’t spend much time thinking about cybersecurity. After all, don’t most cybercriminals focus their efforts on big companies with deep pockets?
The truth is, cybercrime presents a genuine threat to your...
Read Full Story »
Tags: managed IT, mobility, remote working, risk management, small & medium-sized businesses (SMB), tips & training
Posted in: Cybersecurity
March 6th, 2019 by Kevin Box
In late 2013, hackers breached the systems of Fazio Mechanical Services, a heating and ventilation systems contractor. Through the Fazio Mechanical Services breach, the attackers were able to steal the network credentials of the third-largest U.S. retailer...
Read Full Story »
Tags: email, multifunction printers (MFP), risk management, tips & training
Posted in: Cybersecurity
March 4th, 2019 by Function4
No matter what type of business you're in, managing information requires a good portion of your team's time. A robust document management solution can replace ad hoc strategies that take too much time and don't work well in today's information-saturated...
Read Full Story »
Tags: collaboration tools, cost reduction, digital workflows, risk management
Posted in: Document Management
February 27th, 2019 by Function4
If your employees have been using mobile devices for work with no apparent consequences for your organization, should you still consider a mobile device management solution? The answer is yes, especially given the security vulnerabilities widespread...
Read Full Story »
Tags: cost reduction, mobility, risk management
Posted in: Document Management
February 25th, 2019 by Function4
Iconic heists have made and destroyed fortunes. They make great scenes for exciting movie plots. Think of Butch Cassidy and his gang blowing up train tracks and fleeing on horseback with $50,000 in cash. Or consider a thief walking out of the Louvre...
Read Full Story »
Tags: cyberattacks, email, risk management
Posted in: Cybersecurity
February 20th, 2019 by Function4
Is your company adopting more digital processes in the coming year? Forward-thinking leaders recognize the inevitability of digitization and are doing everything they can to update their business processes. While the benefits of switching from paper-based...
Read Full Story »
Tags: digital workflows, managed IT, multifunction printers (MFP), risk management
Posted in: Business Technology
February 18th, 2019 by Brad Yocum
I began my career as a young 20-year-old in the mid-1990s working in the copy, print and imaging industry. At the time, office technology was just in its infancy. Creating a duplicate copy of an image was cutting edge. Sending pictures via fax was innovative....
Read Full Story »
Tags: cyberattacks, email, mobility, risk management
Posted in: Cybersecurity
January 28th, 2019 by Function4
Data breaches are a company’s biggest fear.
If you own a company, the thought of someone stealing your data is probably enough to make you want to cut the cord and take your company offline. Of course, this isn’t practical in today’s economy, as computers...
Read Full Story »
Tags: cyberattacks, email, risk management, small & medium-sized businesses (SMB)
Posted in: Cybersecurity
January 21st, 2019 by Function4
The 21st century has already seen some astonishing advances in the technology sector, with new opportunities coming so fast that many businesses struggle to stay on top of changes.
Mobile device management is one technology solution your organization...
Read Full Story »
Tags: mobility, content & process management, risk management
Posted in: Document Management, Business Technology
January 14th, 2019 by Function4
Should you outsource some or all of your IT responsibilities to a trusted provider? For many small and mid-sized companies, outsourcing to a managed services provider is an excellent way to access benefits not ordinarily available for smaller organizations....
Read Full Story »
Tags: cost reduction, managed IT, risk management, small & medium-sized businesses (SMB)
Posted in: Business Technology
January 7th, 2019 by Function4
We've all experienced the frustration of trying to locate a lost document. Sometimes lost paperwork is just a hassle, but when a critical business document can't be found, the stakes may be much higher.
Here's how a document management system can make...
Read Full Story »
Tags: collaboration tools, cost reduction, digital workflows, remote working, risk management
Posted in: Document Management
December 31st, 2018 by Function4
Have you considered outsourcing the management of your IT infrastructure to a managed IT services partner? Small and medium-sized businesses are among a growing group of organizations recognizing the value provided by partnerships with advanced managed...
Read Full Story »
Tags: cost reduction, managed IT, risk management
Posted in: Business Technology
December 17th, 2018 by Function4
The predictions were accurate—mobile workforce numbers continue to grow as companies realize the value of an agile staff with 24/7 access to business data. Here's why the most successful among these business leaders look to mobile device management to...
Read Full Story »
Tags: cyberattacks, mobility, remote working, risk management
Posted in: Business Technology
December 10th, 2018 by Function4
A great document management solution can speed up your existing business processes, with time savings as high as 40% to 75% depending on your current processes. Since time is still money, you can count on some significant improvements to your bottom...
Read Full Story »
Tags: digital workflows, multifunction printers (MFP), content & process management, risk management
Posted in: Document Management
December 3rd, 2018 by Function4
As a small or medium-sized business (SMB) owner, you wear many hats. One of those responsibilities may be IT security, although you may have a nagging suspicion that your company is not adequately protected. With cyberattacks continuing to escalate,...
Read Full Story »
Tags: data backup and recovery, managed IT, risk management, small & medium-sized businesses (SMB)
Posted in: Business Technology
November 26th, 2018 by Function4
Allowing your employees to use personally-owned mobile devices for work doesn't mean that you have no say in how those devices are used. If you're too hands-off, a simple mistake by an employee could give hackers access to your company's confidential...
Read Full Story »
Tags: managed IT, mobility, remote working, risk management
Posted in: Business Technology
November 19th, 2018 by Function4
If you've been handling all of your IT needs in-house, you may be wondering if it's time to consider outsourcing to a professional Managed IT Services provider. For small and medium-sized businesses (SMBs), outsourcing may seem like a risky financial...
Read Full Story »
Tags: managed IT, risk management, small & medium-sized businesses (SMB)
Posted in: Business Technology
November 12th, 2018 by Function4
Should you keep a technician on staff or outsource to a professional IT security company? For many companies, the latter is the most cost-effective choice. Here's a look at how an IT security company can provide you with 24-hour protection at a cost that's...
Read Full Story »
Tags: cost reduction, email, managed IT, risk management
Posted in: Business Technology
October 29th, 2018 by Function4
manage [man-ij] to bring about or succeed in accomplishing, sometimes despite difficulty or hardship. (Dictionary.com)
How well are you succeeding at managing your IT infrastructure on your own? Are you killing it or are ongoing issues plaguing your...
Read Full Story »
Tags: cost reduction, managed IT, risk management
Posted in: Business Technology
October 22nd, 2018 by Function4
Your employees probably use their personally-owned mobile devices for at least some of their work. They may use them to check email, text co-workers about projects, or put meetings on their calendar. Rather than risk security issues when employees devise...
Read Full Story »
Tags: mobility, content & process management, remote working, risk management
Posted in: Business Technology
October 8th, 2018 by Function4
Social engineering has been around since the first traveling hucksters pitched miracle cures from the back of horse-drawn wagons. Today's social engineering schemes may be a little more sophisticated, but they have the same result—very embarrassed victims...
Read Full Story »
Tags: cyberattacks, email, managed IT, risk management, tips & training
Posted in: Cybersecurity
October 1st, 2018 by Function4
Personal mobile device usage is now so prevalent in company work environments that few question the practice. As more and more BYOD employees enter the workplace, Mobile Device Management professionals provide a wide variety of services to protect confidential...
Read Full Story »
Tags: managed IT, mobility, content & process management, risk management
Posted in: Document Management, Business Technology
September 17th, 2018 by Function4
While most efforts to protect information have to do with stopping outside intruders and malicious attacks, information is vulnerable from the inside as well. Is yours protected?
Protection Through Your Document Management System
Document management...
Read Full Story »
Tags: cyberattacks, data backup and recovery, risk management
Posted in: Document Management
September 10th, 2018 by Function4
Mobile workers are expected to comprise nearly 75% of the workforce in the U.S. within the next two years. The healthcare sector can expect to see a similar trend, and controlling data access will become even more complicated than it is today.
While...
Read Full Story »
Tags: healthcare, managed IT, mobility, risk management
Posted in: Business Technology
August 27th, 2018 by Function4
Access to expert tech support is essential for the modern small business, and you'll need to spend some time researching your IT options. Your organization can't afford to waste money, but cutting corners in critical areas is not a good choice, either....
Read Full Story »
Tags: cost reduction, managed IT, risk management
Posted in: Business Technology
August 20th, 2018 by Function4
How much will it cost your company to recover following a data breach? New research from the Ponemon Institute and IBM paints a sobering picture, with costs increasing by 1.8% in 2017. And here in the U.S., businesses can expect to pay even more than...
Read Full Story »
Tags: cost reduction, cyberattacks, data backup and recovery, managed IT, multifunction printers (MFP), risk management
Posted in: Business Technology
August 6th, 2018 by Function4
Want to get more value from each workday? Mobile device management can help by providing strategies for managing your company's BYOD (bring your own device) and COPE (corporate-owned, personally enabled) mobile strategies. Here's how mobile device management...
Read Full Story »
Tags: email, mobility, multifunction printers (MFP), risk management
Posted in: Business Technology
July 23rd, 2018 by Function4
Owning and operating a business can be all-consuming, with little time left over for distractions; an IT security solution that isn't performing is a distraction you can live without. Allowing someone to manage your system for you may be a perfect solution...
Read Full Story »
Tags: managed IT, mobility, remote working, risk management
Posted in: Business Technology
July 9th, 2018 by Function4
A recent international survey by Check Point Software Technologies made it clear that businesses must step up their game when it comes to mobile device management. Their unsettling research of 850 firms revealed:
No business was left untouched—each...
Read Full Story »
Tags: cyberattacks, mobility, risk management
Posted in: Cybersecurity
June 18th, 2018 by Function4
If you're worried about data security (and who isn't these days?), a document management system can give you the peace of mind you're seeking. Document management also increases efficiency, saves time, and reduces operating costs.
When added to the built-in...
Read Full Story »
Tags: data backup and recovery, digital workflows, encryption, managed IT, risk management
Posted in: Document Management
June 11th, 2018 by Function4
With security breaches continuously on the rise, SMBs have been unable to escape the fallout. In fact, more than 60% of small businesses were the victim of some form of cybercrime in 2017. Since you would rather be in the 40% of companies who didn't...
Read Full Story »
Tags: cyberattacks, email, risk management, small & medium-sized businesses (SMB), tips & training
Posted in: Cybersecurity
May 7th, 2018 by Function4
Document management can help your company in countless ways. It saves time, money, and stress, all by streamlining and strengthening the ways you deal with paper—but that's a pretty general statement, isn't it? Today we'll look at three specific...
Read Full Story »
Tags: collaboration tools, content & process management, risk management
Posted in: Document Management
April 30th, 2018 by Function4
Managed IT services provide countless benefits that help improve efficiency, budget-friendliness, and morale across any company--but what can it do for your company? Here's a quick look at just a few reasons why managed IT is right for you.
A Crash-Course...
Read Full Story »
Tags: cost reduction, managed IT, content & process management, risk management
Posted in: Business Technology