October 17th, 2022 by Paul Perez
For some organizations, print marketing is their primary avenue for distributing information to the public. Though digital marketing has unleashed new marketing methods such as SMS, Email, and Social-Media, print still plays a large role, and its effectiveness...
Read Full Story »
Tags: cost reduction, email, printing, vendor / partner relationships
Posted in: Managed Print Services
September 8th, 2022 by Function4
Leading MTSP Shares Why Email Is an Easy Way to Destroy A Company’s Network
SUGAR LAND, TX - Function4, a leading managed technology services provider (MTSP), recently announced that they are protecting small to mid-sized businesses (SMBs) with...
Read Full Story »
Tags: cyber security, cyberattacks, email, services, solutions
Posted in: Press Release
June 7th, 2021 by Darcy Mekis
Cybersecurity is a growing concern for organizations all over the world. A single attack can lead to thousands or even millions in losses, and cybercriminals continue to come up with more sophisticated methods of attack. Ransomware and malware...
Read Full Story »
Tags: cyberattacks, data backup and recovery, email, ransomware, small & medium-sized businesses (SMB), tips & training
Posted in: Cybersecurity
August 5th, 2020 by Ed Hoffmann
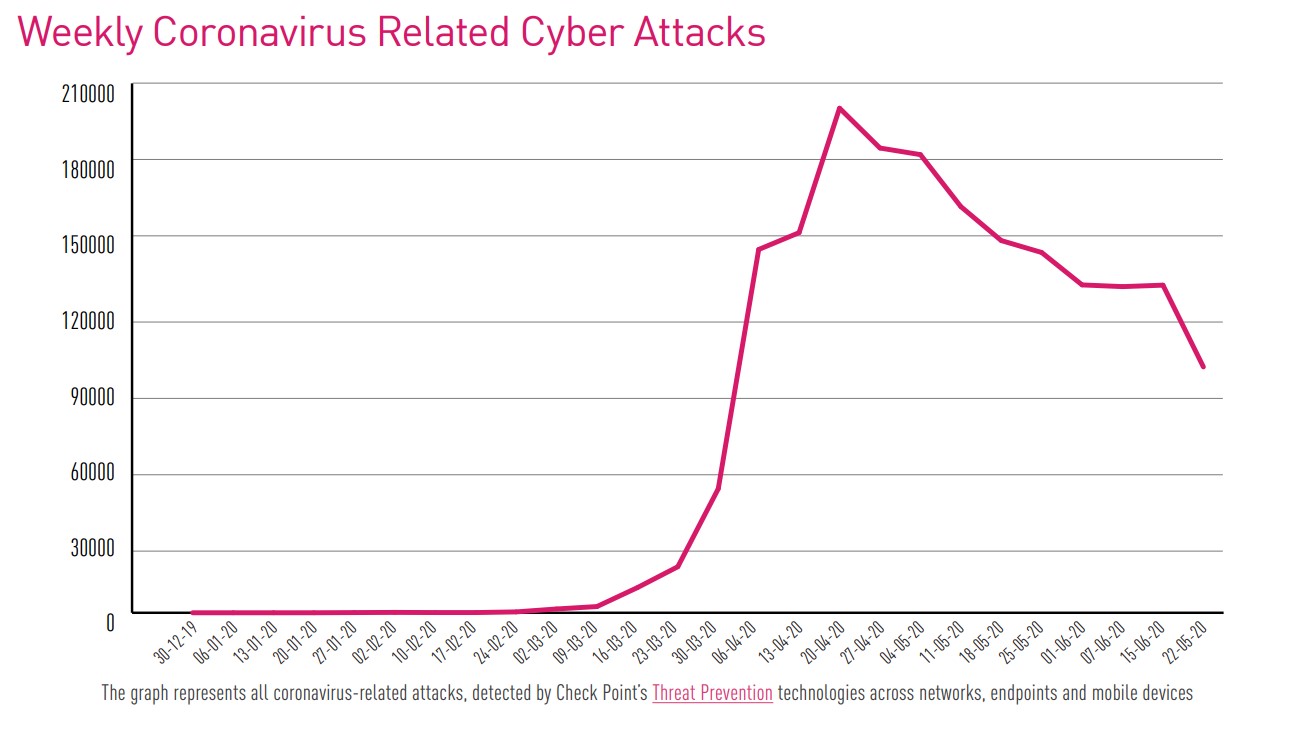
Organizations today face an ever-increasing number of cyber threats. The rapid growth of criminal software development, coupled with the cybersecurity skills shortage, has also contributed to the rise in cyber-attacks.
The COVID-19 pandemic has had...
Read Full Story »
Tags: COVID-19, cyberattacks, email, ransomware, tips & training
Posted in: Cybersecurity
April 22nd, 2019 by Function4
Your company’s biggest cybersecurity weakness may be your employees. Your staff likely means well, but if they aren’t trained in proper cybersecurity procedures, their innocent errors could cost you a small fortune. But you can keep your company both...
Read Full Story »
Tags: antivirus, email, mobility, ransomware, remote working, tips & training
Posted in: Cybersecurity
March 18th, 2019 by Function4
It doesn’t matter if you’re running a small-town business or a large, multinational corporation. If you own a business of any size, you’re at risk for threats such as cyberattacks and data breaches. Cyberthreats do not discriminate.
For a business,...
Read Full Story »
Tags: cloud-based, data backup and recovery, email, mobility, tips & training
Posted in: Cybersecurity
March 6th, 2019 by Kevin Box
In late 2013, hackers breached the systems of Fazio Mechanical Services, a heating and ventilation systems contractor. Through the Fazio Mechanical Services breach, the attackers were able to steal the network credentials of the third-largest U.S. retailer...
Read Full Story »
Tags: email, multifunction printers (MFP), risk management, tips & training
Posted in: Cybersecurity
February 25th, 2019 by Function4
Iconic heists have made and destroyed fortunes. They make great scenes for exciting movie plots. Think of Butch Cassidy and his gang blowing up train tracks and fleeing on horseback with $50,000 in cash. Or consider a thief walking out of the Louvre...
Read Full Story »
Tags: cyberattacks, email, risk management
Posted in: Cybersecurity
February 18th, 2019 by Brad Yocum
I began my career as a young 20-year-old in the mid-1990s working in the copy, print and imaging industry. At the time, office technology was just in its infancy. Creating a duplicate copy of an image was cutting edge. Sending pictures via fax was innovative....
Read Full Story »
Tags: cyberattacks, email, mobility, risk management
Posted in: Cybersecurity
February 13th, 2019 by Function4
Mass-scale AI-driven cyberattacks could be headed your way soon. Artificial intelligence (AI) is already effectively deployed as a way to detect malware and combat spam, so it stands to reason that AI will soon be a favored tool for hackers.
With AI...
Read Full Story »
Tags: cyberattacks, email, managed IT
Posted in: Cybersecurity
January 28th, 2019 by Function4
Data breaches are a company’s biggest fear.
If you own a company, the thought of someone stealing your data is probably enough to make you want to cut the cord and take your company offline. Of course, this isn’t practical in today’s economy, as computers...
Read Full Story »
Tags: cyberattacks, email, risk management, small & medium-sized businesses (SMB)
Posted in: Cybersecurity
November 12th, 2018 by Function4
Should you keep a technician on staff or outsource to a professional IT security company? For many companies, the latter is the most cost-effective choice. Here's a look at how an IT security company can provide you with 24-hour protection at a cost that's...
Read Full Story »
Tags: cost reduction, email, managed IT, risk management
Posted in: Business Technology
October 8th, 2018 by Function4
Social engineering has been around since the first traveling hucksters pitched miracle cures from the back of horse-drawn wagons. Today's social engineering schemes may be a little more sophisticated, but they have the same result—very embarrassed victims...
Read Full Story »
Tags: cyberattacks, email, managed IT, risk management, tips & training
Posted in: Cybersecurity
August 6th, 2018 by Function4
Want to get more value from each workday? Mobile device management can help by providing strategies for managing your company's BYOD (bring your own device) and COPE (corporate-owned, personally enabled) mobile strategies. Here's how mobile device management...
Read Full Story »
Tags: email, mobility, multifunction printers (MFP), risk management
Posted in: Business Technology
June 11th, 2018 by Function4
With security breaches continuously on the rise, SMBs have been unable to escape the fallout. In fact, more than 60% of small businesses were the victim of some form of cybercrime in 2017. Since you would rather be in the 40% of companies who didn't...
Read Full Story »
Tags: cyberattacks, email, risk management, small & medium-sized businesses (SMB), tips & training
Posted in: Cybersecurity